In the ever-evolving cybersecurity landscape, traditional security measures are continually being challenged by sophisticated threats. Organizations increasingly recognize the need to adopt more dynamic, adaptive security frameworks to protect their sensitive data and systems. One such framework that has gained significant traction is the Zero Trust Architecture (ZTA). This article explores the concept of Zero Trust, its components, and how it can enhance an organization’s IT security posture.
Understanding Zero Trust Architecture
Zero Trust is a strategic cybersecurity paradigm that eliminates the concept of trust from an organization’s network architecture. Rooted in the principle of “never trust, always verify,” Zero Trust protects modern digital environments by leveraging network segmentation, preventing lateral movement, providing Layer 7 threat prevention, and simplifying granular user-access control.
The traditional security model, called the castle-and-moat approach, assumes that everything inside an organization’s network can be trusted. However, this assumption is flawed in today’s threat landscape, where threats can originate outside and inside the network. Zero Trust recognizes that trust is a vulnerability. Once on the network, users – including threat actors and malicious insiders – can move laterally and access or exfiltrate sensitive data unless proper controls are in place.
Critical Components of Zero Trust Architecture
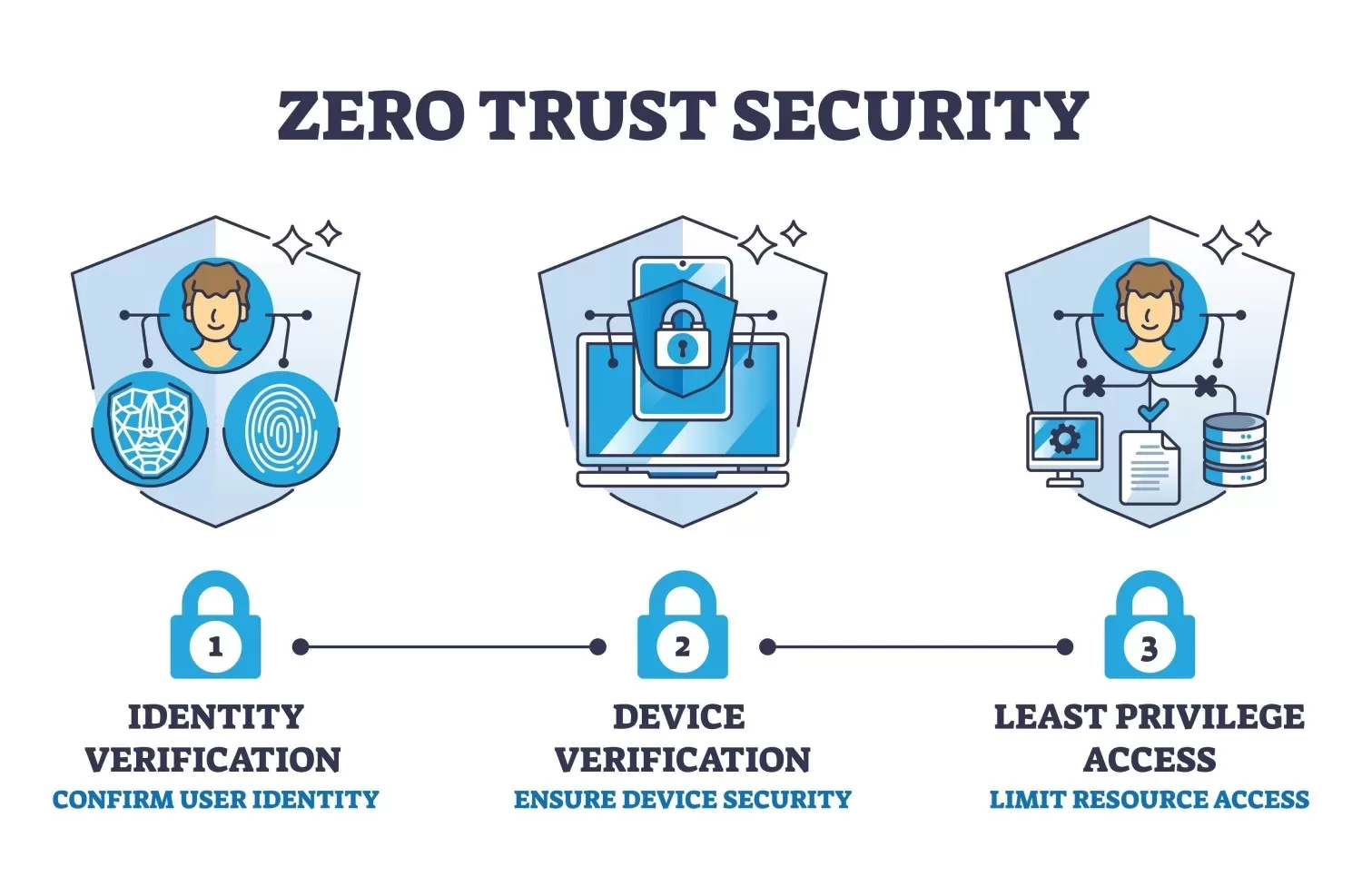
Implementing a Zero Trust Architecture requires a holistic approach to network security that integrates several key components:
1. Identity Verification
Zero-trust systems require strict identity verification for every user and device trying to access network resources. This often involves multi-factor authentication (MFA), rigorous identity management, and least privilege access principles.
2. Device Security
It is crucial to ensure that all devices attempting to access the network are secure. This includes enforcing security policies, performing regular security patches, and monitoring for signs of compromise.
3. Microsegmentation
Micro-segmentation involves breaking up security perimeters into small zones to maintain access to separate network parts. This means if an attacker compromises one segment, they won’t automatically gain access to other parts of the network.
4. Least Privilege Access Control
This principle involves limiting user access rights to the minimum necessary to perform their job functions. This helps reduce the attack surface, and the potential damage that compromised credentials or insider threats can do.
5. Real-time Threat Detection and Response
Zero Trust architectures rely on advanced threat detection and response strategies that monitor and analyze data about network traffic and user behaviors to identify and respond to threats in real-time.
6. Data Security
Protecting data at rest and in transit using encryption, tokenization, and other protective technologies ensures that data breaches are less impactful.
Benefits of Implementing Zero Trust
Adopting Zero Trust can offer numerous benefits to an organization, including:
- Enhanced Security Posture: By verifying all users and devices and granting access on a need-to-know basis, Zero Trust minimizes the opportunities for attackers to gain access to the network and move laterally.
- Reduced Data Breach Impact: Microsegmentation and least privilege lessen the extent to which a breach can spread through an organization’s network.
- Compliance with Regulations: Many data protection regulations recommend or require controls that are intrinsic to Zero Trust, such as data encryption and access controls.
- Improved Visibility and Control: Zero Trust solutions offer greater visibility into devices and users on the network, thereby improving the control over who accesses what resources.
Challenges in Implementing Zero Trust
While the benefits are clear, transitioning to a zero-trust architecture has challenges. These include:
- Complexity of Implementation: Deploying Zero Trust can be complex, particularly in organizations with legacy systems and sprawling, heterogeneous networks.
- Cultural Shift: Moving to a Zero Trust model involves a shift in organizational culture and mindset from a default trust to a default verify stance.
- Resource-Intensive: The initial setup and ongoing management of a Zero Trust environment can be resource-intensive in terms of time, personnel, and finances.
Conclusion
As cyber threats continue to evolve, so must our IT security approaches. Zero Trust Architecture offers a robust framework for safeguarding against sophisticated cyberattacks by adhering to the principle of never trust, always verify. While implementing Zero Trust can be challenging, the potential benefits of enhanced security, compliance, and data protection make it a compelling choice for organizations aiming to fortify their cybersecurity defenses.